EN - eLearning - EC-Council Certified Incident Handler (ECIH) v3
Master the skills to identify, contain, and minimize cyber incidents.
Download Brochure
If you want to learn more about the training, check out the official training brochure!
What you'll get
- One (1) Year Access to the e-courseware.
- Six (6) months access to EC-Council's official online lab environment.
- Certification or Exam voucher valid for a period of one (1) year.
- Certification and examination fees are included in the price of the training course.
- Expert instructor-led training modules with streaming video presentations and learning supplements for an all-inclusive training program that provides the benefits of classroom training at your own pace with a validity of one (1) year.
- 20% reduction on the first year subscription for our all-in-one ISMS/GRC management solution
Official ECC-Reseller-Certificate
What is the ECIH program
EC-Council's Certified Incident Handler program equips students with the knowledge, skills, and abilities to effectively prepare for, deal with, and eradicate threats and threat actors in an incident. This program provides the entire process of incident handling and response and hands-on labs that teach the tactical procedures and techniques required to effectively plan, record, triage, notify and contain. Students will learn the handling of various types of incidents, risk assessment methodologies, as well as laws and policies related to incident handling.
After attending the course, students will be able to create IH&R policies and deal with different types of security incidents such as malware, email security, network security, web application security, cloud security, and insider threat-related incidents.
The E|CIH (EC-Council Certified Incident Handler) also covers post incident activities such as containment, eradication, evidence gathering and forensic analysis, leading to prosecution or countermeasures to ensure the incident is not repeated. The E|CIH is a method-driven course that provides a holistic approach covering vast concepts related to organizational IH&R, from preparing/planning the incident handling response process to recovering organizational assets from the impact of security incidents. These concepts are essential for handling and responding to security incidents to protect organizations from future threats or attacks.
With over 95 advanced labs, 800 tools covered, and exposure to incident handling activities on many different operating systems, E|CIH provides a well-rounded, but tactical approach to planning for and dealing with cyber incidents.
The E|CIH program addresses all stages involved in the IH&R process, and this attention toward a realistic and futuristic approach makes E|CIH one of the most comprehensive IH&R-related certifications in the market today
Learn the 9 stages of Incident Handling and Response Process
Key features
95
Hands-on labs
800+
Incident handing and response tools
1600 Pages of student manual
Who should take this course?
- Incident Handler
- Incident Responder
- Incident Response Consultant/Associate/Analyst/Engineer/Specialist/Expert/Manager
- CSIRT Analyst/Engineer/Manager
- Information Security Associate/Analyst/Engineer/Specialist/Manager
- Cyber Defense Security Consultant/Associate/Analyst
- IT Security Operations Center Analyst (SOC Analyst/Engineer)
- Cyber Forensic Investigator/Consultant/Analyst/Manager
- Digital Forensic Analyst
- Cyber Risk Vulnerability Analyst/Manager
- Cyber Intelligence Analyst and Cyber Security Threat Analyst/Specialist
- Cyber Security Incident Response Team Lead
- Penetration Tester
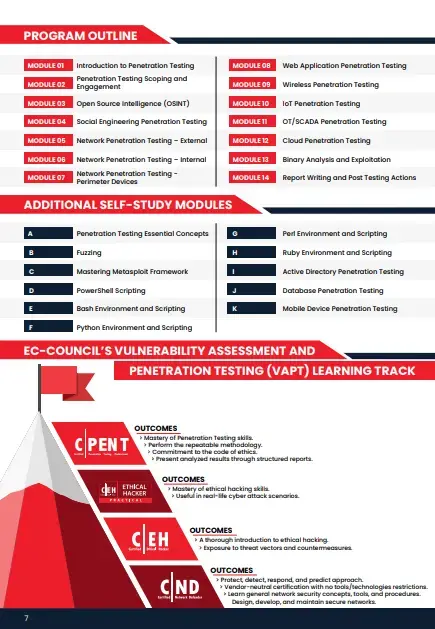
Course Outline
- MODULE 01: INTRODUCTION TO INCIDENT HANDLING AND RESPONSE
- Understand Information Security Threats and Attack Vectors
- Explain Various Attack and Defense Frameworks
- Understand Information Security Concepts
- Understand Information Security Incidents
- Understand the Incident Management Process
- Understand Incident Response Automation and Orchestration
- Describe Various Incident Handling and Response Best Practices
- Explain Various Standards Related to Incident Handling and Response
- Explain Various Cybersecurity Frameworks
- Understand Incident Handling Laws and Legal Compliance
- MODULE 02: INCIDENT HANDLING AND RESPONSE PROCESS
- Understand Incident Handling and Response (IH&R) Process
- Explain Preparation Steps for Incident Handling and Response
- Understand Incident Recording and Assignment
- Understand Incident Triage
- Explain the Process of Notification
- Understand the Process of Containment
- Describe Evidence Gathering and Forensic Analysis
- Explain the Process of Eradication
- Understand the Process of Recovery
- Describe Various Post-Incident Activities
- Explain the Importance of Information Sharing Activities
- MODULE 03: FIRST RESPONSE
- Explain the Concept of First Response
- Understand the Process of Securing and Documenting the Crime Scene
- Understand the Process of Collecting Evidence at the Crime Scene
- Explain the Process for Preserving, Packaging, and Transporting Evidence
- MODULE 04: HANDLING AND RESPONDING TO MALWARE INCIDENTS
- Understand the Handling of Malware Incidents
- Explain Preparation for Handling Malware Incidents
- Understand Detection of Malware Incidents
- Explain Containment of Malware Incidents
- Describe How to Perform Malware Analysis
- Understand Eradication of Malware Incidents
- Explain Recovery after Malware Incidents
- Understand the Handling of Malware Incidents - Case Study
- Describe Best Practices against Malware Incidents
- MODULE 05: HANDLING AND RESPONDING TO EMAIL SECURITY INCIDENTS
- Understand Email Security Incidents
- Explain Preparation Steps for Handling Email Security Incidents
- Understand Detection and Containment of Email Security Incidents
- Understand Analysis of Email Security Incidents
- Explain Eradication of Email Security Incidents
- Understand the Process of Recovery after Email Security Incidents
- Understand the Handling of Email Security Incidents - Case Study
- Explain Best Practices against Email Security Incidents
- MODULE 06: HANDLING AND RESPONDING TO NETWORK SECURITY INCIDENTS
- Understand the Handling of Network Security Incidents
- Prepare to Handle Network Security Incidents
- Understand Detection and Validation of Network Security Incidents
- Understand the Handling of Unauthorized Access Incidents
- Understand the Handling of Inappropriate Usage Incidents
- Understand the Handling of Denial-of-Service Incidents
- Understand the Handling of Wireless Network Security Incidents
- Understand the Handling of Network Security Incidents - Case Study
- Describe Best Practices against Network Security Incidents
- MODULE 07: HANDLING AND RESPONDING TO WEB APPLICATION SECURITY INCIDENTS
- Understand the Handling of Web Application Incidents
- Explain Preparation for Handling Web Application Security Incidents
- Understand Detection and Containment of Web Application Security Incidents
- Explain Analysis of Web Application Security Incidents
- Understand Eradication of Web Application Security Incidents
- Explain Recovery after Web Application Security Incidents
- Understand the Handling of Web Application Security Incidents - Case Study
- Describe Best Practices for Securing Web Applications
- MODULE 08: HANDLING AND RESPONDING TO CLOUD SECURITY INCIDENTS
- Understand the Handling of Cloud Security Incidents
- Explain Various Steps Involved in Handling Cloud Security Incidents
- Understand How to Handle Azure Security Incidents
- Understand How to Handle AWS Security Incidents
- Understand How to Handle Google Cloud Security Incidents
- Understand the Handling of Cloud Security Incidents - Case Study
- Explain Best Practices against Cloud Security Incidents
- MODULE 09: HANDLING AND RESPONDING TO INSIDER THREATS
- Understand the Handling of Insider Threats
- Explain Preparation Steps for Handling Insider Threats
- Understand Detection and Containment of Insider Threats
- Explain Analysis of Insider Threats
- Understand Eradication of Insider Threats
- Understand the Process of Recovery after Insider Attacks
- Understand the Handling of Insider Threats - Case Study
- Describe Best Practices against Insider Threats
- MODULE 10: HANDLING AND RESPONDING TO ENDPOINT SECURITY INCIDENTS
- Understand the Handling of Endpoint Security Incidents
- Explain the Handling of Mobile-based Security Incidents
- Explain the Handling of IoT-based Security Incidents
- Explain the Handling of OT-based Security Incidents
- Understand the Handling of Endpoint Security Incidents - Case Study
Achieving the CSA Certification Credential
Exam Title: Certified Threat Intelligence Analyst
Exam Code: 212-89
Number of questions: 100
Durations: 3 hours
Availability: Online
Passing score: See here
- Live remote proctor for online ECC Exam option.
Testimonial
Ask any question about our products
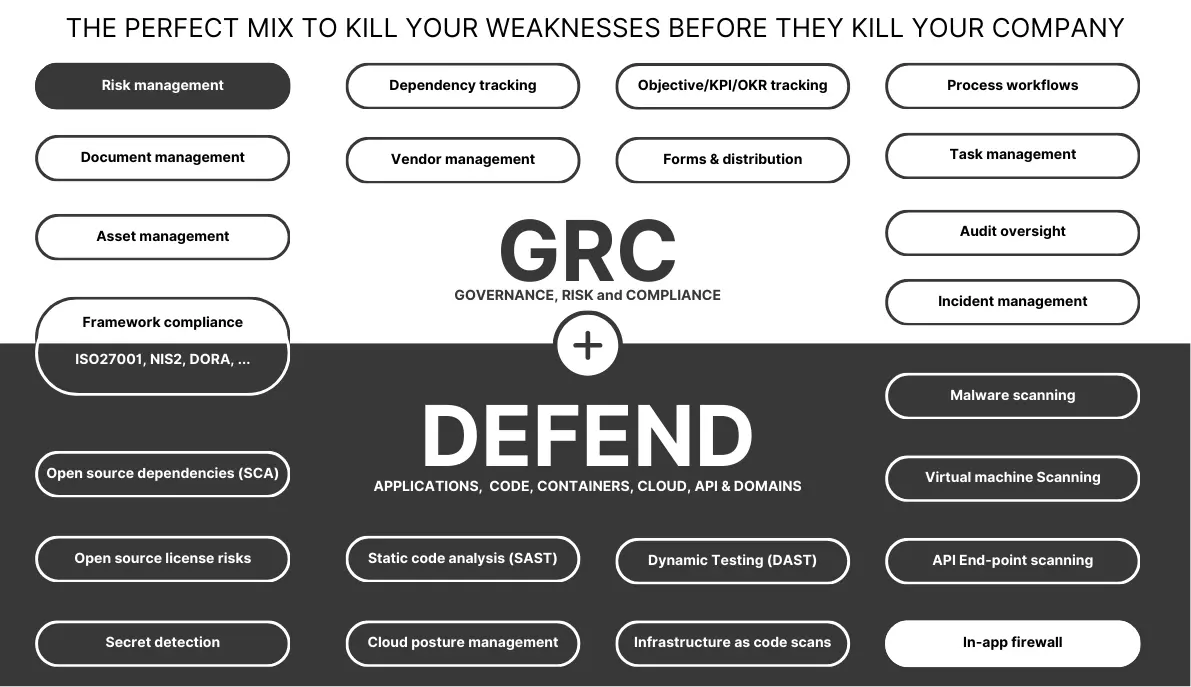
Streamline your GRC work using our all-in-one management solution and get access to our network of local specialists
Start your free account
%20v3?unique=068bc5a)